The breach, revealed in documents provided to The Intercept, gave the agencies the power to secretly monitor a large portion of the world’s cellular communications, which experts said violated international laws.
Mark Rumold, staff attorney at the Electronic Frontier Foundation, said there was no doubt that the spy agencies had violated Dutch law and were in all probability violating laws in many other territories when they used the hacked keys.
“They have the functional equivalent of our house keys,” he said. “That has serious implications for privacy not just here in the US but internationally.”
The scale of the hack and its international reach will likely reopen wounds in the diplomatic community. The Obama administration faced intense criticism from Germany, Brazil and other nations following the Snowden leaks and has been working hard recently to repair the damage.
Previous documents disclosed by the Guardian showed Angela Merkel, the German chancellor, was the target of an NSA spying campaign, a revelation that has soured US-German relations. Brazil’s president Dilma Rousseff has already accused the NSA of violating international law.
“It’s a big breach,” Matthew Green, a cryptologist at the Johns Hopkins Information Security Institute, told the Guardian. “The problem is that the attacks could still be ongoing.”
Gemalto, the company targeted by the spy agencies, produces 2bn sim cards per year for clients including AT&T, Sprint, T-Mobile and Verizon. The Netherlands company operates in 85 countries around the world and provides cards to some 450 wireless network providers globally.
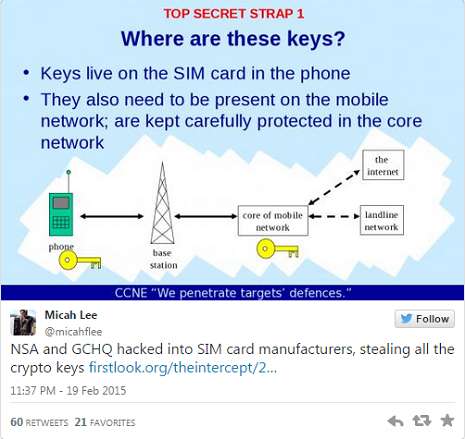
The stolen encryption keys would allow intelligence agencies to monitor mobile communications without the approval or knowledge of telecom companies and foreign governments.
Chris Soghoian, principal technologist at the American Civil Liberties Union, told the Guardian the hack would allow spies to “put an aerial up on the embassy in Berlin and listen in to anyone’s calls in the area”.
Calls made on 3G and 4G mobile networks are encrypted. But with the keys, which a GCHQ slide described as living “in the phone”, spies could access any communication made on a device unless its owner uses an extra layer of encryption.
Soghoian said the latest Snowden revelations meant that it was difficult for anyone to trust the security of a mobile phone. “It is very unlikely that this is an issue that is going to be fixed anytime soon,” he said. “There is no reason for people to trust AT&T, Verizon or anyone at this point. Their systems are hopelessly insecure.”
“The real value of this is that it allows bulk surveillance of telecoms without anyone getting caught,” Soghoian said of hacks like the one at Gemalto, which he said would allow the spy agencies to target “whoever they wanted”.
“In countries where the government will not cooperate, that’s very useful,” he said. “It’s also very useful in countries where the government would help. Germany would allow spy on a suspected terrorist but not on [Angela] Merkel.”
Paul Beverly, a Gemalto executive vice president, told The Intercept that the company was totally oblivious to the penetration of its systems. “I’m disturbed, quite concerned that this has happened,” he said. “The most important thing for me is to understand exactly how this was done, so we can take every measure to ensure that it doesn’t happen again.”
According to the Snowden documents, Gemalto was targeted by the Mobile Handset Exploitation Team (MHET), a unit formed by the NSA and GCHQ in April 2010 to target vulnerabilities in cell phones.
The Intercept reports that in one GCHQ slide, the British intelligence agency boasted it had planted malware – malignant software – on several of Gemalto’s computers, giving GHCQ access to “their entire network”.
Green, from Johns Hopkins, said the scale of the hack – “apparently a huge percentage” of the sim cards at Gemalto – would mean a massive replacement process.
“Suppliers are going to have to tighten up their practices before anyone can think about fixing this,” he told the Guardian, “and that’s going to be a nightmare.”
The keys were obtained after a clandestine operation targeting the email and Facebook accounts of Gemalto employees and other telecom executives. GCHQ operatives singled out key individuals within Gemalto and then hacked their private accounts.
One Gemalto employee in Thailand was identified as “a good place to start” after he was observed sending encrypted files, a move the agents suggested meant he was sending valuable information.
More about:








-1780923278.jpg&h=190&w=280&zc=1&q=100)